-
Notifications
You must be signed in to change notification settings - Fork 177
View File Certificates
Violet Hansen edited this page Jan 16, 2025
·
3 revisions
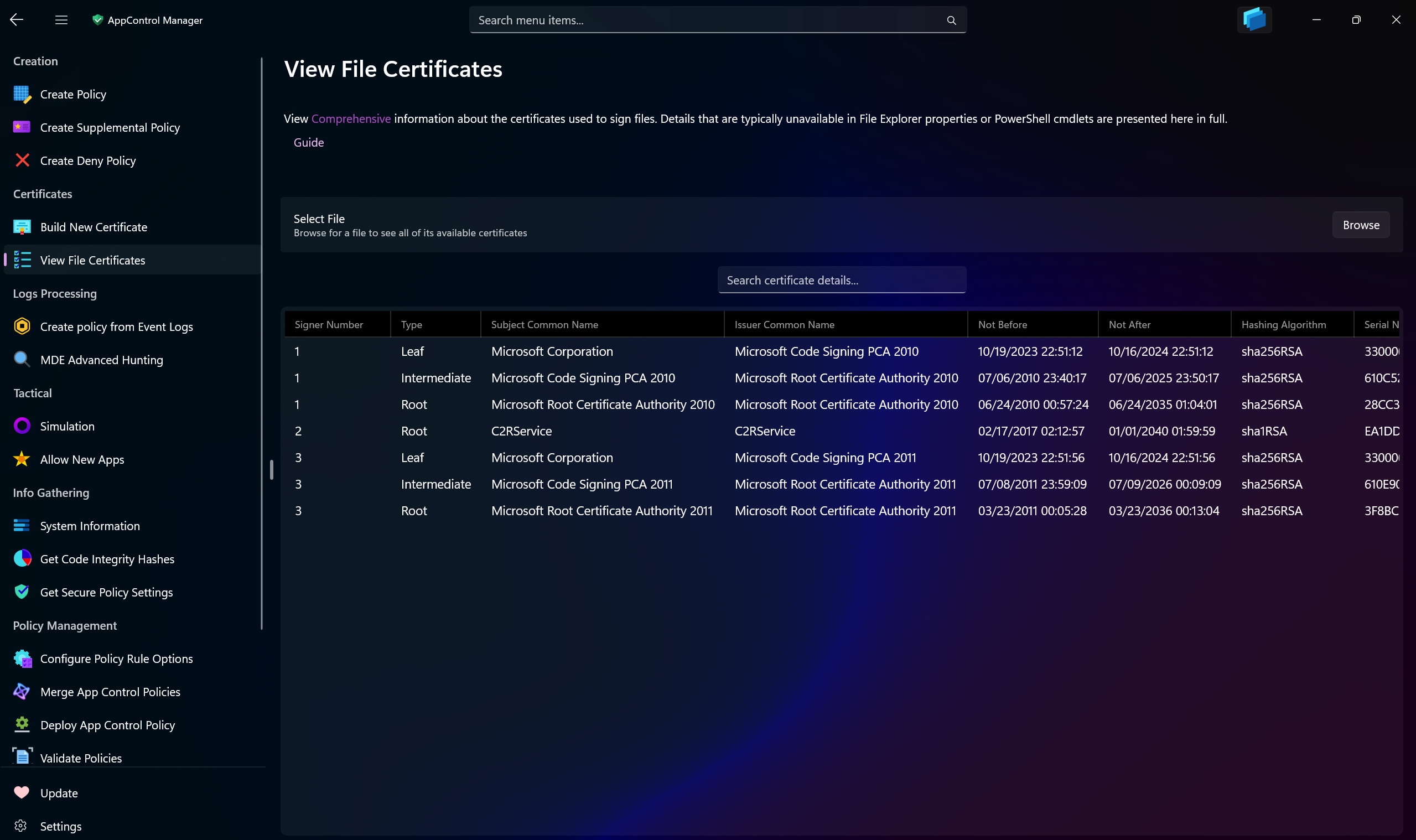
Use this AppControl Manager page to view highly detailed information about the certificates that are embedded in the signed files on your system. This feature will display the complete chains of all of the signers of a signed file.
Tip
This feature allows you to verify the signing certificates in the .CIP files of signed App Control policies as well.
Note
This feature supports displaying the certificates of the files signed by Security Catalogs.
The following data is displayed for each member of the certificate chain:
| Name | Description |
|---|---|
| Signer Number | A unique identifier assigned to the certificate's signer. If the file is signed by multiple certificates, then each of them will have a different number, allowing you to easily differentiate between them. |
| Type | Specifies the type of certificate: root, intermediate, or leaf. |
| Subject Common Name | The Common Name (CN) field in the certificate's subject. |
| Issuer Common Name | The Common Name (CN) field of the certificate's issuer. |
| Not Before | The starting date and time when the certificate becomes valid. |
| Not After | The expiration date and time when the certificate is no longer valid. |
| Hashing Algorithm | The cryptographic algorithm used to create a hash of the certificate's contents. |
| Serial Number | A unique numeric identifier assigned to the certificate by the issuing Certificate Authority (CA). |
| Thumbprint | A unique hash value (fingerprint) derived from the entire certificate, used to verify integrity. |
| TBS Hash | The hash of the "To Be Signed" (TBS) portion of the certificate, ensuring its integrity before signing. |
| Extension OIDs | Object Identifiers (OIDs) that define optional extensions, such as key usage, policies, or constraints. |
- Create AppControl Policy
- Create Supplemental Policy
- System Information
- Configure Policy Rule Options
- Simulation
- Allow New Apps
- Build New Certificate
- Create Policy From Event Logs
- Create Policy From MDE Advanced Hunting
- Create Deny Policy
- Merge App Control Policies
- Deploy App Control Policy
- Get Code Integrity Hashes
- Get Secure Policy Settings
- Update
- Sidebar
- Validate Policies
- View File Certificates
- Introduction
- How To Generate Audit Logs via App Control Policies
- How To Create an App Control Supplemental Policy
- The Strength of Signed App Control Policies
- How To Upload App Control Policies To Intune Using AppControl Manager
- How To Create and Maintain Strict Kernel‐Mode App Control Policy
- How to Create an App Control Deny Policy
- App Control Notes
- How to use Windows Server to Create App Control Code Signing Certificate
- Fast and Automatic Microsoft Recommended Driver Block Rules updates
- App Control policy for BYOVD Kernel mode only protection
- EKUs in App Control for Business Policies
- App Control Rule Levels Comparison and Guide
- Script Enforcement and PowerShell Constrained Language Mode in App Control Policies
- How to Use Microsoft Defender for Endpoint Advanced Hunting With App Control
- App Control Frequently Asked Questions (FAQs)
- Create Bootable USB flash drive with no 3rd party tools
- Event Viewer
- Group Policy
- How to compact your OS and free up extra space
- Hyper V
- Overrides for Microsoft Security Baseline
- Git GitHub Desktop and Mandatory ASLR
- Signed and Verified commits with GitHub desktop
- About TLS, DNS, Encryption and OPSEC concepts
- Things to do when clean installing Windows
- Comparison of security benchmarks
- BitLocker, TPM and Pluton | What Are They and How Do They Work
- How to Detect Changes in User and Local Machine Certificate Stores in Real Time Using PowerShell
- Cloning Personal and Enterprise Repositories Using GitHub Desktop
- Only a Small Portion of The Windows OS Security Apparatus
- Rethinking Trust: Advanced Security Measures for High‐Stakes Systems
- Clean Source principle, Azure and Privileged Access Workstations
- How to Securely Connect to Azure VMs and Use RDP
- Basic PowerShell tricks and notes
- Basic PowerShell tricks and notes Part 2
- Basic PowerShell tricks and notes Part 3
- Basic PowerShell tricks and notes Part 4
- Basic PowerShell tricks and notes Part 5
- How To Access All Stream Outputs From Thread Jobs In PowerShell In Real Time
- PowerShell Best Practices To Follow When Coding
- How To Asynchronously Access All Stream Outputs From Background Jobs In PowerShell
- Powershell Dynamic Parameters and How to Add Them to the Get‐Help Syntax
- RunSpaces In PowerShell
- How To Use Reflection And Prevent Using Internal & Private C# Methods in PowerShell
